Il noto dev CrashSerious in giornata è tornato a farsi sentire rilasciando una nuova applicazione che prende il nome di UNSIG.
Grazie ad essa, si possono decriptare i file in formato SIG, i quali sono rimasti gli unici ,in giro per la rete, a non essere stati “scoperti”. Era già stato rilasciato un tool che permetteva tale procedura, gli autori erano gli an0nimous , ma purtroppo il programma riportava un trojan.
Ma andiamo a vedere le parole ufficiali dello sviluppatore…
Good Day everyone,
This time I figured I’d release something I’ve had a while but didn’t think it would be useful to anyone. However, several people I mentioned it to were quite interested in the tool, so I figured I’d bring it out as a release. I’ll be honest, I have ulterior motives…
We used the last month’s winnings to purchase Cobra dongles for the entire team. This month, we’re planning on using the donation (should you decide this is worthy to vote for…) to purchase flasher’s to protect our PS3’s from a Cobra/TB brick.
This release is a tool that will decrypt (and then also re-encrypt) the SIG files that were leaked in the CEX-DEX packages earlier this year and also the files released by an0nymous a month or so ago. The SIG files have not gotten a lot of attention, maybe because no one could read them.
However, that’s about to change.
Why should you care about this release?
Because the SIG files are a list of instructions for the objective suites application to interface to the lv2diag.self files that were leaked with the previous Objective Suites stuff.
Very low level stuff, for the most part, that will actually let you modify settings in the PS3 firmware. With the proper information (the piece that math has kept to himself), CEX to DEX conversions are not only possible– but are a reality. Things like reading (and writing) the ECID, IDPS, KIBAN_ID, and console serial number… just to name a few.
Basically, it’s a very low level trusted connection that is made and the PS3 does what you ask it to via Objective Suites.
How do I use this?
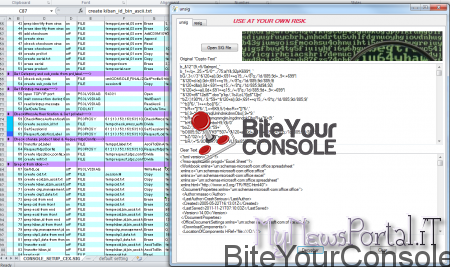
To un-SIG—- In the unsig tab, select “Open SIG File” and the file’s encrypted contents will be loaded and displayed in the first text box. Then Select “Decypher” and the Decyphered text will be displayed in the second. It will also create an Microsoft Excel readable (and editable) file in the same folder with “.XLS” added as an extension.
To Re-SIG—- In the resig tab, follow the same exact process as above except select the xls file. The process works the same, except the file saved as a “.SIG” extension.
Keep in mind, while this tool will create a valid SIG file that Objective Suites *CAN* use. It should initially be used as a tool to learn more about the SIG file format.
If you find something useful in reversing the SIG files, do me a favor— put it in the wiki and give back to the scene, would ya? You can start off by looking here -> SIG File Format – PS3 Development Wiki
What we were attempting to convey last month is that, honestly, people need to work together more.
No one person is going to break the PS3 wide open. GeoHot, didn’t do it by himself.
Kakaroto, won’t by himself. And neither will math. It’s time to work together as a collective group, and not as a bunch of disfunctional individuals.
Together we are strong, separately we are just weak.
ONE FINAL NOTE: the last release of Objective Suites that an0nymous leaked had a trojan in it— BE AWARE and BEWARE!! I know ps3hax released a cleaned one and the first release was virus free.
Make sure you get that one if you run the Objective Suites application. HOWEVER, the SIG files in the An0nymous release are new and of value to the scene.
I file SIG sono dei file che possono permettere di modificare le impostazioni dei firmware della PS3. Fino ad oggi tali file non sono mai stati studiati affondo perchè mancava un programma come questo.
Chissà se una volta decriptati daranno ai developer del materiale utile per poter arrivare a una soluzione per i nostri backup.
Stay Tuned



![[Scena PS3] Rilasciato irisMAN v4.91.1 ora con exFAT Manager aggiornato alla versione 0.9](https://www.biteyourconsole.net/wp-content/uploads/IRISMAN-1.jpg)
![[Scena PS3] Rilasciato Simple File Manager MOD v0.9](https://www.biteyourconsole.net/wp-content/uploads/SimpleFileManager2-238x178.webp)

![[Scena PS4] Rilasciato PPPwnUI 3.30a Mod by Aldostools](https://www.biteyourconsole.net/wp-content/uploads/PPPwnUI1-1-100x75.webp)


![[Scena Ps3] PSChannel v1.10 rilasciato](https://www.biteyourconsole.net/wp-content/uploads/PSC110.png)
![[Scena PS3] Aggiunto il supporto per montare giochi da remoto in ps3netsrv attraverso la versione Lite di webMAN Mod](https://www.biteyourconsole.net/wp-content/uploads/PS3NetServer1-100x75.jpg)
![[Scena PS3] Rilasciato HAN Toolbox v0.5](https://www.biteyourconsole.net/wp-content/uploads/HAN007.jpg)